Starbucks has confirmed a data breach that exposed sensitive personal information belonging to hundreds of employees after attackers gained unauthorized access to internal accounts.
Quick Summary – TLDR:
- Starbucks disclosed a data breach affecting 889 individuals after attackers accessed employee accounts.
- Phishing websites impersonating the Partner Central portal were used to steal login credentials.
- Exposed information includes names, Social Security numbers, dates of birth, and financial account details.
- Starbucks is offering two years of identity protection and credit monitoring services to affected individuals.
What Happened?
Starbucks discovered suspicious activity involving its Partner Central employee portal on February 6, 2026. An investigation later revealed that attackers accessed several employee accounts between January 19 and February 11 after stealing login credentials through phishing websites that mimicked the company’s internal portal.
The breach ultimately exposed sensitive personal information belonging to 889 individuals, prompting the company to notify affected employees and law enforcement authorities.
⚠️ Starbucks Data Breach – Hundreds of Users’ Personal Data Exposed
— Cyber Security News (@The_Cyber_News) March 13, 2026
Source: https://t.co/EBC98WSx7p
Starbucks Corporation has confirmed a data breach affecting an undisclosed number of its employees, exposing highly sensitive personal and financial information after… pic.twitter.com/Azc2yc8BYo
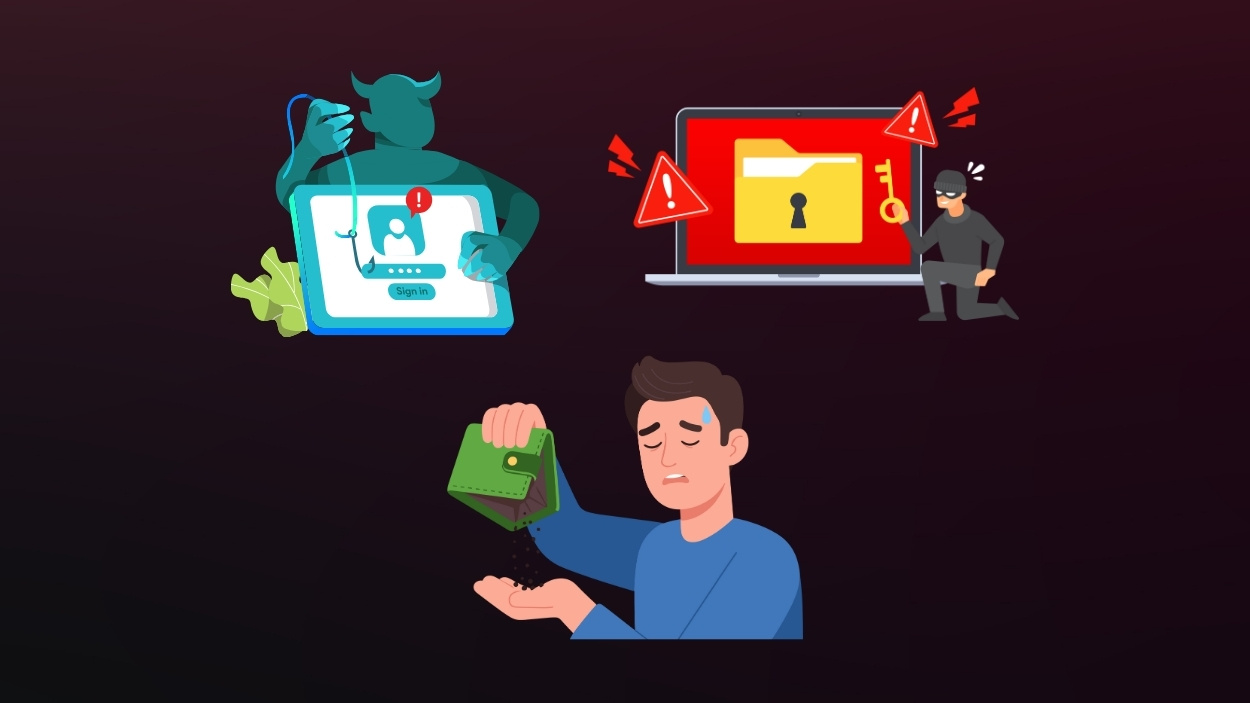
Attackers Used Phishing Sites to Capture Credentials
According to the company’s investigation, the attackers created websites that impersonated Starbucks Partner Central, the internal platform employees use to manage payroll, benefits, and HR information.
Employees who visited the fake websites unknowingly entered their login credentials, allowing attackers to capture the information and access legitimate accounts.
Once inside the system, the unauthorized party was able to view data stored in the compromised accounts. The Partner Central portal contains sensitive employment records, making it a valuable target for credential phishing campaigns.
Starbucks said the compromised accounts were used to access employee information before the activity was detected and contained.
Personal and Financial Data Was Exposed
The breach exposed several categories of highly sensitive personal and financial information stored within employee accounts.
Potentially exposed information includes:
- Full names
- Social Security numbers
- Dates of birth
- Financial account and routing numbers
Because the compromised information includes Social Security numbers and banking details, affected individuals could face risks such as identity theft or financial fraud if the data is misused.
Security experts often warn that even limited personal identifiers can be used for phishing attacks, social engineering schemes, or fraudulent financial activity.
Timeline of the Incident
The breach unfolded over several weeks before it was discovered.
Key events include:
- January 19 to February 11, 2026: Unauthorized access occurred within Partner Central accounts.
- February 6, 2026: Starbucks detected suspicious activity and launched an investigation.
- March 10, 2026: The company began notifying affected individuals through written notices.
The breach disclosure was also submitted to the Maine Attorney General’s Office, which is required when residents of the state are affected. Five residents of Maine were included in the group of impacted individuals.
Starbucks Responds to the Security Incident
After discovering the data breach, Starbucks said it immediately began an internal investigation and brought in external cybersecurity experts to help determine the scope of the incident.
The company also notified law enforcement agencies and took steps to strengthen security controls related to access to the Partner Central platform.
Starbucks said it is offering 24 months of free identity protection services to affected individuals through Experian identity protection programs. These services include:
- Credit monitoring
- Identity theft detection alerts
- Fraud resolution support
- Assistance with identity restoration if needed
Affected employees have also been advised to monitor their financial accounts and credit reports for suspicious activity.
Previous Security Incidents Add to Concerns
While this breach impacted employee accounts rather than customer systems, Starbucks has previously faced security related incidents.
In 2022, the company’s Singapore division disclosed a breach affecting more than 219000 customers after a third party vendor storing customer data was compromised.
More recently, the company was also affected by disruptions linked to a 2024 ransomware attack targeting Blue Yonder, a supply chain software provider used by Starbucks.
These incidents reflect broader challenges companies face when protecting sensitive data across complex digital systems.
SQ Magazine Takeaway
I think this incident shows how credential phishing remains one of the easiest ways for attackers to break into corporate systems. Even a company as large and technologically mature as Starbucks can be vulnerable when employees are tricked into giving away login information.
What stands out to me is that the breach did not require advanced hacking techniques. It simply relied on fake websites that looked like the real employee portal. That is a reminder that human focused attacks remain one of the biggest cybersecurity risks for companies today.
Organizations handling employee or customer data need stronger protections such as multi-factor authentication and phishing resistant login systems to prevent similar incidents in the future.